Recent disruptions to Poland's railway system have unveiled an unexpected vulnerability. While initial speculations pointed to an elaborate cyberattack given Russia's hacking history, investigations reveal the attackers utilized a very basic RADIOSTOP function to halt trains across Poland. This attack can executed by anyone who is willing to spend $30. Interestingly, it seems like EU legislation forced Poland to adopt a standard that is vulnerable to this incredibly simple attack.
What Happened?
Over two days, more than 20 Polish trains were interrupted by what many described as a “cyberattack.” These disruptions, accompanied by the Russian national anthem and excerpts from a speech by Russian president Vladimir Putin, were significant due to Poland's railway's role in aiding NATO-supported Ukraine against Russia's invasion.
The RADIOSTOP Function Explained
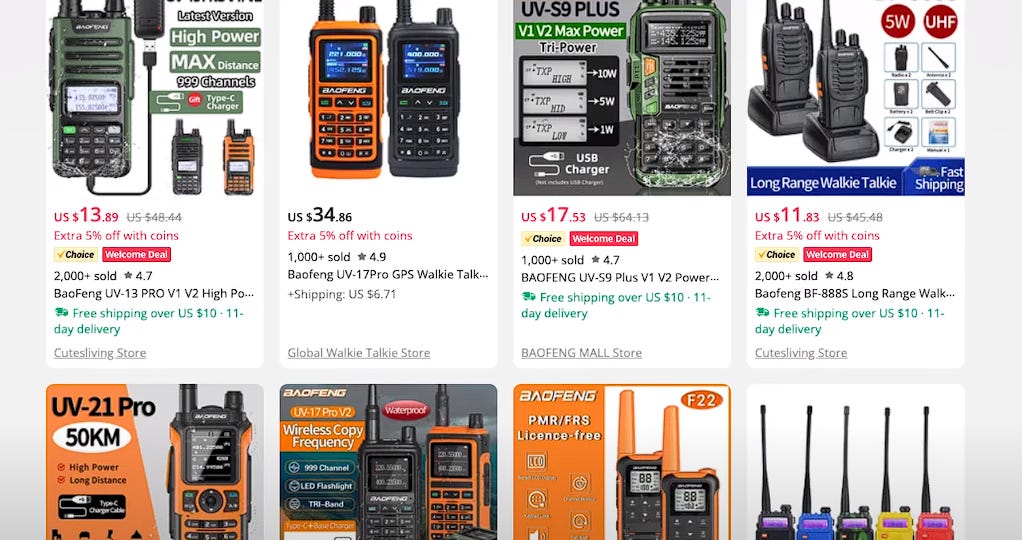
The culprits essentially leveraged an open secret in the train community. Using off-the-shelf radio equipment that costs as little as $30, they broadcasted a “radio-stop” command to the trains. This command, which has been detailed in various forums and YouTube videos for years, is a simple sequence of three acoustic tones at a specific frequency (150.100 MHz). Once received, the train's emergency stop function is activated. These frequencies and the functions are public knowledge and are part of EU legislation.
Purpose: A built-in safety feature, designed for both track-side and on-board use, allowing trains to be remotely stopped in emergencies.
Activation: Triggered by a single sealed button.
Functionality: On activation, it releases a series of tones, followed by a sequence of specific frequencies. Receiving these frequencies twice consecutively triggers the train's emergency braking system.
Mechanism: The braking is facilitated via a valve in a secondary pneumatic channel, separate from the main Automatic Warning System.
How It Was Exploited
Saboteurs, with basic off-the-shelf radio equipment for $30, broadcasted the required frequency sequence to trigger the RADIOSTOP function. Poland's train system, lacking encryption or authentication for these commands, was left vulnerable. This simple, yet effective exploitation brought numerous trains to a standstill.
In essence, this event underscores the importance of holistic security measures, catering not just to sophisticated cyber threats, but also to basic system vulnerabilities. What is worse, it seems like Poland was forced to adopt these vulnerable standards by EU legislation. The EU has to seriously re-think standard-setting if it does not want to be vulnerable to Russian attacks.